Entry-Level Cybersecurity Analyst Resume
This resume example effectively demonstrates the skills and accomplishments of career changers, making it an excellent resource for those transitioning into the role of cybersecurity analyst.
Why this resume works:
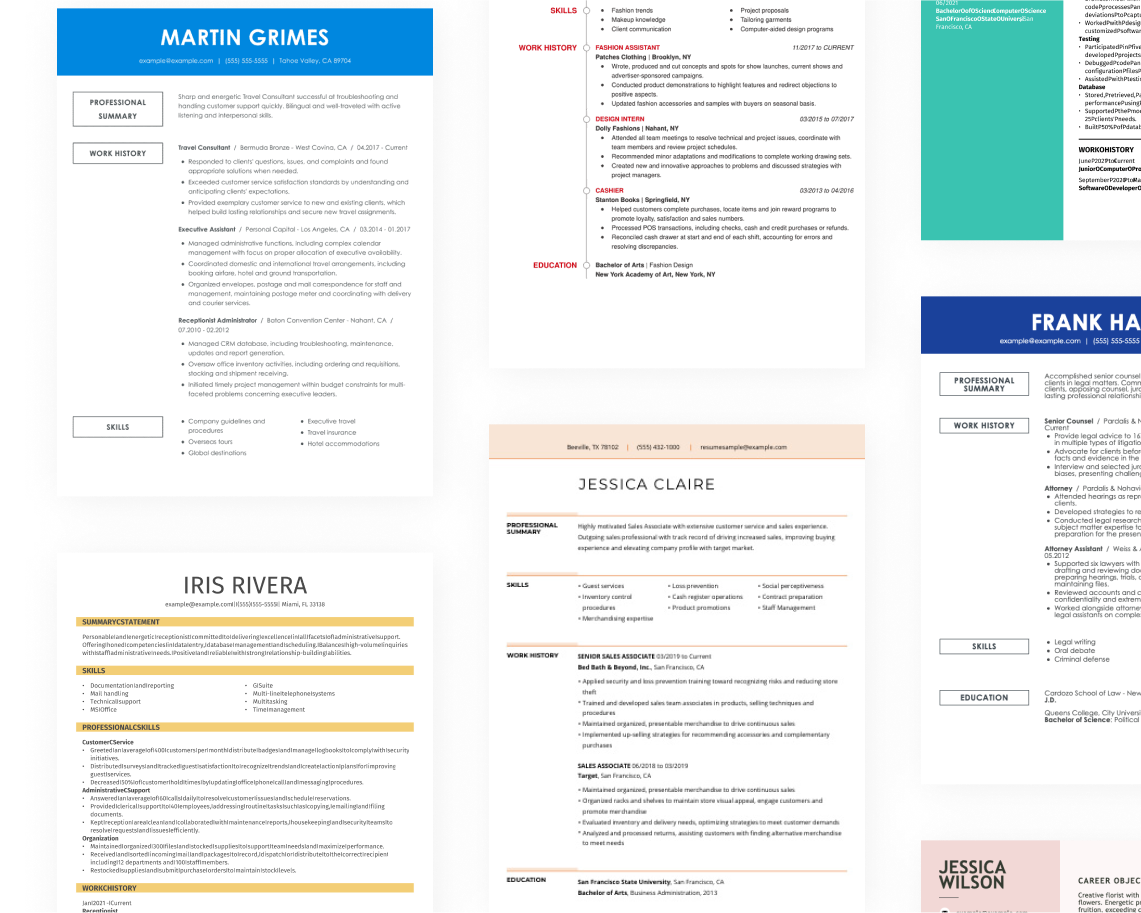
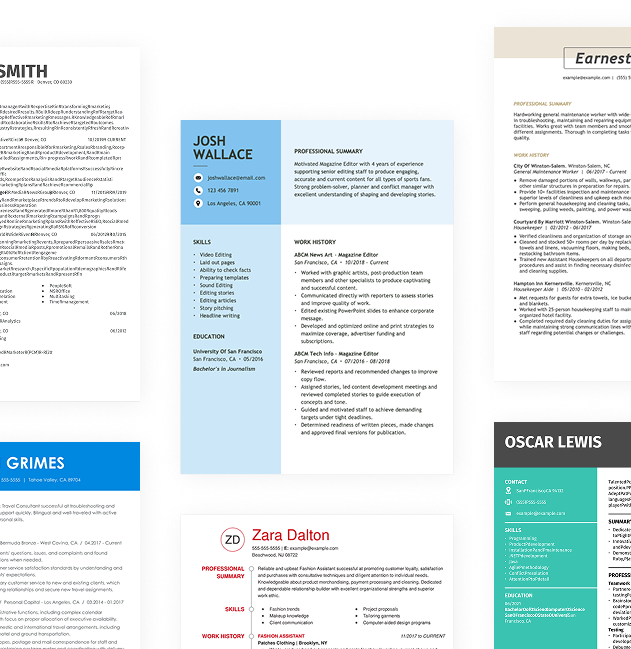
A skills-focused resume format is beneficial for aspiring cybersecurity analysts, those returning to the field, or career changers. This approach allows applicants to emphasize valuable skills like network security, risk assessment, and incident response rather than dwelling on limited experience or employment gaps. Highlighting these competencies can improve their appeal to potential employers.
Mid-Career Cybersecurity Analyst Resume
This resume example is perfect for cybersecurity analysts with experience seeking to advance their careers by highlighting significant achievements and specialized skills in a rapidly evolving field.
Why this resume works:
Mid-career cybersecurity analysts can highlight achievements such as decreasing security incidents by 30% through improved monitoring systems or successfully training 300 employees in cybersecurity best practices. They may also mention leading initiatives that reduced breach recovery times by 50%, significantly improving overall organizational security posture.
Experienced Cybersecurity Analyst Resume
This cybersecurity analyst resume is perfect for experienced professionals seeking senior roles, showcasing extensive skills in threat management and leadership capabilities.
Why this resume works:
Leadership roles and advanced certifications underscore the ability to manage complex scenarios.
Looking for something else?
Create Your Standout Resume Today
Use our resume examples for inspiration on organization, color, and design—and learn how to effectively summarize your cybersecurity analyst skills and experience with confidence.
How to Write a Cybersecurity Analyst Resume
Learning how to write a resume is important for cybersecurity analysts to highlight their unique value and expertise instead of merely listing technical skills. By emphasizing your problem-solving abilities and project experiences, you can set yourself apart in the competitive field of cybersecurity.
In the following sections, we’ll guide you through writing a resume step-by-step, offering essential resume tips on formatting, showcasing certifications, and presenting your experience effectively.
Start with your contact info
The header section contains all your contact information, prominently displayed at the top of your resume. Start with your name in a bold and larger font to ensure it catches the recruiter's eye immediately. Choosing a clean, professional layout will improve readability and help your application stand out among others.
Next, include essential contact details such as your email address, phone number, and location; city and state are sufficient for recruiters. This information is vital for communication and helps applicant tracking systems identify job seekers based on their geographical relevance.
Lastly, consider adding links to certifications relevant to cybersecurity or any online portfolios showcasing your projects and skills. These additional resources can significantly bolster your application by demonstrating your expertise and commitment to staying current in the field of cybersecurity, making you a more attractive applicant.
Write a strong professional summary
A professional summary on a cybersecurity analyst resume serves as your initial introduction, appearing right after your contact details. This section offers a snapshot of your qualifications and sets the tone for your application.
In this brief overview, highlight relevant skills and experiences while expressing your passion for cybersecurity. Tailoring this summary to the specific role you’re pursuing can significantly improve its impact and relevance.
To craft an effective summary, consider reviewing resume summary examples from other resumes in the field. These examples can provide inspiration and guidance on how to structure and articulate your own unique narrative.
Strong vs weak cybersecurity analyst summary
Strong
"Results-driven cybersecurity analyst with over four years of experience in threat detection and incident response. Proven expertise in vulnerability assessment, security monitoring, and compliance audits, successfully reducing security breaches by 30% within the first year. Certified in CISSP and CEH, recognized for developing effective security protocols that improve organizational resilience."
Why this example works: This summary effectively describes the applicant, showcases measurable achievements such as a 30% reduction in breaches, highlights key skills like threat detection and compliance audits, and incorporates relevant keywords found in cybersecurity job descriptions.
Weak
"Cybersecurity analyst seeking a position where I can use my skills to protect information. I have some experience in the field and enjoy working with technology."
Why this example doesn't work: This summary is weak due to its vague language and fails to highlight specific technical skills, relevant experience, or measurable achievements that would demonstrate the applicant's qualifications.
Craft a personal mission statement that highlights your commitment to protecting information and maintaining trust, aligning with your employer's values of integrity and security. Emphasize how your analytical skills and proactive approach improve organizational resilience beyond mere technical expertise.
Share your work history
Your work history is, arguably, the central and most important part of your resume. List your most recent roles in reverse chronological order. If you’ve held numerous positions, select the ones most relevant to the job you’re applying for.
When listing your work history, focus on:
- Job title and company name
- Dates of employment (month and year)
- Key responsibilities (What did you do on a daily basis?)
- Achievements and contributions (What did you accomplish? Did you improve processes, reduce costs, or increase efficiency?)
- Measurable results (Use numbers when possible, such as "reduced patient wait times by 15%.")
Finally, when describing your achievements, use action verbs to make your work history come alive.
Strong vs weak cybersecurity analyst work history
Strong
Cybersecurity Analyst, TechSecure Solutions
2019–2023
- Conducted over 500 vulnerability assessments, identifying critical security risks and reducing potential breaches by 40%.
- Developed incident response protocols that decreased average response time to security incidents from 24 hours to 4 hours.
- Led a team in implementing a new firewall system, improving network security and achieving compliance with industry standards.
Why this example works: A strong work history for a cybersecurity analyst highlights specific achievements and quantifiable results. By detailing tasks and demonstrating technical skill alongside leadership capabilities, it creates a compelling narrative of your expertise in safeguarding information systems.
Weak
Cybersecurity analyst
Tech Solutions Inc.
- Monitored systems and fixed issues.
- Helped with security reports.
Why this example doesn't work: This entry is ineffective as it lacks detail about the specific cybersecurity tasks performed, provides no context regarding the technologies used or threats addressed, and does not mention any outcomes or metrics.
To improve your visibility in the cybersecurity field, add your resume to LinkedIn. Use industry-specific keywords and showcase relevant certifications in your profile summary to attract recruiters seeking top talent for their teams.
Highlight your key skills
The skills section of your resume is essential for demonstrating your strengths as a cybersecurity analyst. Here's a rundown of different skill sets and their significance in the field:
- Soft skills are personal attributes that illustrate how you collaborate with others—such as critical thinking, attention to detail, and effective communication. For cybersecurity analysts, traits like teamwork and adaptability are important as they help in identifying threats and responding swiftly to ensure robust security measures.
- Hard skills refer to specialized technical abilities acquired through training, education, or hands-on experience. For a cybersecurity analyst, examples include network security protocols, intrusion detection systems, vulnerability assessment tools, and incident response strategies.
- Technical skills for a cybersecurity analyst include expertise with security software and technologies. Core tools involve intrusion detection systems, such as Snort, firewall management solutions like Palo Alto Networks, and threat intelligence platforms like Recorded Future.
For a cybersecurity analyst resume, new professionals should position their skills section at the top to highlight their abilities despite limited experience. In contrast, seasoned analysts can place this section after work history, showcasing how their experience demonstrates those skills effectively.
Top 15 skills for your cybersecurity analyst resume
When developing your resume, it's important to showcase skills that align with the demands of a cybersecurity analyst. Balance technical abilities, such as threat analysis and network security, with essential soft skills like problem-solving and communication. Including transferable skills is also important, as they demonstrate your adaptability in different situations.
Here’s a list of the top 15 most popular skills for cybersecurity analysts based on insights from JobHero users. These skills will help you present yourself effectively and highlight what employers value most in this dynamic field.
Build your education section
The education section of your resume should reflect your experience and the expectations of the cybersecurity industry. For seasoned professionals, it is often more beneficial to emphasize your work history and accomplishments rather than your educational background. In such cases, consider placing the education section further down or omitting it entirely if you have substantial relevant experience.
Conversely, for recent graduates or individuals entering specialized areas within cybersecurity, education becomes a key asset. Highlight your degree prominently at the top of your resume, and include any relevant coursework, projects, or certifications that showcase your technical skills and knowledge in the field.
This focus on education will help you stand out among peers who may not have as extensive a professional background. Tailoring this section effectively can improve your candidacy significantly in competitive job markets.
20 action verbs to add to your resume
In a cybersecurity analyst resume, using action verbs improves clarity and engagement. These verbs effectively showcase your experience, making your accomplishments stand out in a competitive field.
Prioritize action verbs that align with the specific skills required in job postings. This tailored approach not only highlights relevant capabilities but also demonstrates your understanding of the role's demands.
- Analyzed
- Secured
- Investigated
- Identified
- Mitigated
- Improved
- Audited
- Trained
- Tested
- Facilitated
- Reviewed
- Developed
- Optimized
- Advised
- Directed
- Responded
- Engaged
- Supported
- Certified
- Reported
Consider additional resume sections
While your core resume provides the most critical information, adding targeted sections can showcase your unique qualifications. These sections help hiring managers quickly identify your skills, certifications, and achievements beyond standard resume sections.
Here are optional sections we tend to see on cybersecurity analyst resumes:
- Technical proficiencies: List specific tools, programming languages, or technologies you are proficient in (e.g., SIEM tools, Python, etc.) to demonstrate your technical abilities.
- Certifications: Detail relevant certifications such as CISSP, CEH, or CompTIA Security+ that validate your expertise in cybersecurity.
- Projects and accomplishments: Highlight significant projects you've led or contributed to that improved security posture or resolved vulnerabilities.
- Professional development: Outline any relevant training sessions, workshops, or courses taken to stay updated with industry best practices.
- Memberships and affiliations: Include memberships in organizations like ISACA or (ISC)² that reflect your commitment to the cybersecurity community.
5 Tips for Formatting Your Resume
Proper resume formatting is important for job seekers as it improves readability and keeps recruiters engaged. Using ATS-friendly resume templates can significantly improve your chances of passing applicant tracking systems while ensuring your qualifications shine through.
1. Watch your line spacing and margins
Proper spacing helps your resume look clean and organized, allowing recruiters to easily navigate through your experiences and skills. With the right spacing, each section of your resume can stand out without overwhelming the reader:
- Set margins between 0.5" to 1", ensuring a neat border.
- Opt for single spacing between paragraphs to maintain consistency.
- Use 1.5" or double-space between sections for clear separation.
2. Use a professional font
Choosing the resume font that fits your resume is essential since it conveys professionalism and attention to detail. Consider these solid font choices:
- Helvetica
- Garamond
- Verdana
- Cambria
- Trebuchet MS
- Book Antiqua
Consider using a slightly more stylized font for your name at the top to give it a distinctive flair that catches the eye.
3. Organize your resume sections
A resume for a cybersecurity analyst should be clear and well-organized. Use bullet points to outline your key responsibilities and achievements in a concise manner. Start each bullet with a strong action verb, such as "Analyzed" or "Implemented," to convey your active role. For example, "Identified vulnerabilities leading to a 40% reduction in security incidents" showcases both your efforts and their impact.
Highlight measurable accomplishments to demonstrate the value you bring. Instead of vague descriptions, provide concrete data: "Developed automated monitoring systems that decreased response time by 50%" illustrates your effectiveness in improving processes.
To ensure your resume is ATS-friendly, use an ATS resume checker. This tool can help you verify that your formatting is compliant with automated systems, increasing the likelihood of getting noticed by hiring managers in the competitive cybersecurity field.
4. Use colors and design
In the fast-evolving field of cybersecurity, a well-crafted resume can truly set you apart. While a straightforward resume is easy to digest, incorporating color and design elements adds character and directs attention to your key skills.
Begin by selecting pre-made resume templates that cater to your style. The combination resume format works particularly well for cybersecurity analysts, as it allows you to feature a colored sidebar that highlights your technical skills prominently alongside your experience.
Next, choose a professional color scheme. Opt for colors like deep blue or dark gray, which evoke trust and security—key traits in the cybersecurity industry. These colors can be used subtly across section headings or borders.
Avoid overly bright colors that may distract from the content or appear unprofessional. Additionally, steer clear of color schemes associated with rival companies or those that compromise readability. Instead, focus on creating an engaging yet polished presentation of your qualifications that reflects your expertise in cybersecurity.
How to use color in creative fields
As a cybersecurity analyst, presenting your skills clearly is important. Your resume should highlight your technical expertise while maintaining a clean and professional layout. Use concise bullet points to showcase your achievements and relevant certifications, ensuring that each line communicates value.
Incorporate visual elements subtly, like icons for certifications or a streamlined format that guides the reader's eye. While creativity can improve appeal, it's vital to keep it aligned with industry standards—cybersecurity firms typically favor straightforward designs over flashy graphics. For instance, a more traditional security company may appreciate a classic font, whereas a tech startup might be open to innovative layouts.
Keep in mind that clarity should always take precedence over style.
5. Keep your resume length to 1-2 pages
Resumes should typically be one page long. This length is ideal because recruiters often have limited time to review each document, making clarity and brevity essential for capturing their attention. Focus on including only the most relevant experiences and skills that align with the job you are pursuing. Avoid listing similar responsibilities across multiple roles to keep your resume concise.
In some cases, extending your resume to two pages may be appropriate, particularly for seasoned professionals applying for high-level positions or those in academia who require a CV. In these scenarios, you can elaborate on significant achievements and contributions while maintaining a clear structure.
FAQ
Do I need to include a cover letter with my resume?
Writing a cover letter can significantly improve your job application, even if it’s not explicitly required. It allows you to showcase your personality and clarify how your skills align with the position. This additional context can make a memorable impression on hiring managers.
To help you craft the perfect cover letter, explore our collection of cover letter examples that cater to various industries and roles. Additionally, when you're ready to create your own, our Cover Letter Builder offers step-by-step assistance to ensure you present yourself in the best light.
What is the best resume format?
Choosing the right resume format depends on your unique situation and goals. The three main formats are chronological, functional, and combination, each serving different types of job seekers effectively.
The chronological format is ideal for those with extensive work history since it emphasizes experience. In contrast, the functional format focuses on transferable skills and education, making it suitable for recent graduates or those changing careers. Lastly, the combination format merges both approaches, offering a well-rounded view that benefits mid-career professionals or individuals transitioning between industries.
How long should my Cybersecurity Analyst resume be?
As a cybersecurity analyst, your resume should ideally be one page. Hiring managers often sift through numerous applications quickly, so a concise format helps highlight your key skills and experience effectively.
Emphasize your most relevant roles in cybersecurity, certifications like CISSP or CEH, and technical skills that align with the job description. Avoid including outdated technologies or extensive details about non-cybersecurity positions that do not add value to your application.
Consider a two-page resume if you have significant experience in advanced roles, such as senior analyst or manager positions. In these cases, showcasing your comprehensive background and achievements can justify the extra length.
Do I need to include references on my resume?
Including references on your resume is usually not needed. However, if you have particularly strong endorsements from respected professionals in the field, it may be worthwhile to add them. Just be prepared to provide them upon request instead of listing them upfront.
Build a custom resume in minutes with our professional templates and expert tips.