- Featured in:
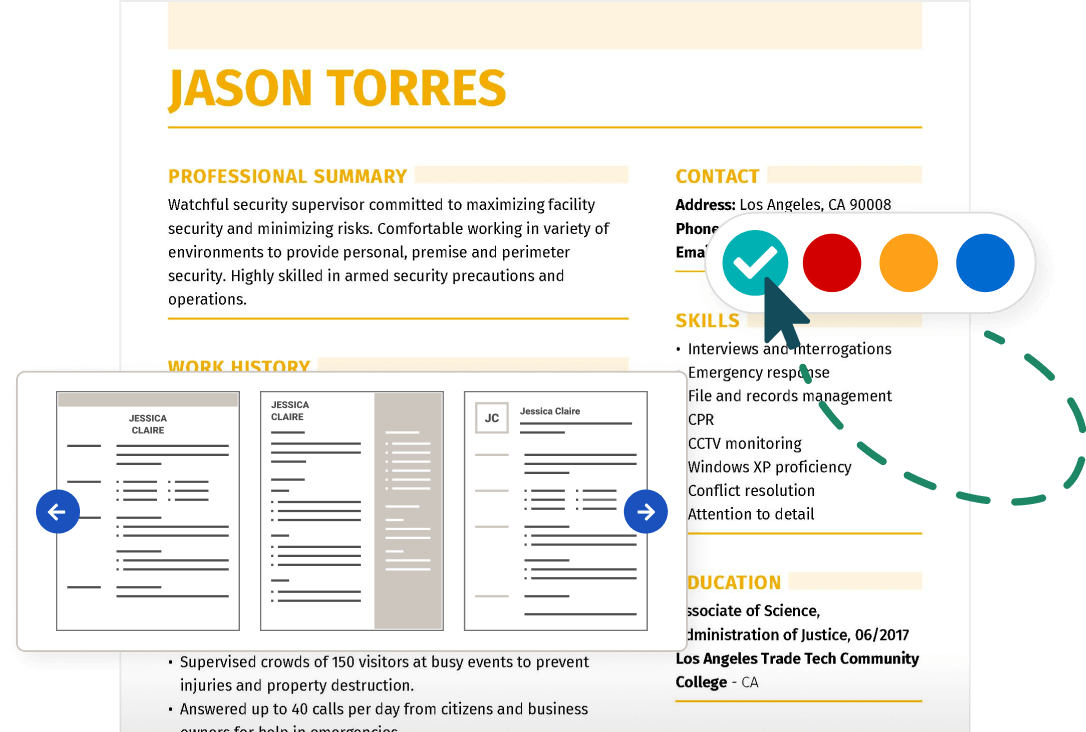
Additional Information Technology Resume Samples
IT Security Specialist Resume Samples
No results found
0-5 years of experience
Monitored networks for vulnerabilities. Interfaced with corporate, regional, and local executives weekly. Authored business analysis reports for executive management. Performed risk assessment reviews for internal clients and external vendors. Performed corporate penetration testing using Backtrack. Managed RSA security tokens as well as measures to prevent viruses and malware. Provided insight to corporate leadership regarding security concepts and framework. Maintained documentation and audit procedures. Played an integral role in enterprise-wide security deployment and process development.
- Earned a 100% rating on IT Audits for Sarbanes Oxley (SOX) and Payment Card Industry (PCI).
- Streamlined processes to effectively support over 3600 employees in multiple locations.
- Served as Lead IT Security Project Manager for large corporate deployments.
- Created regional security measures, policies, and procedures to support multiple locations in the region performing as one entity. Developed disaster recovery plans and processes.
- Designed a Security Access Request Process for users in the Midwest Region to request access, termination notices, and hardware and software.
- Ensured compliance with PCI and SOX auditing requirements by implementing regional procedures.
- Performed duties as Information Security Knowledge Expert.
6-10 years of experience
Investigates breaches and improper use of BLS computer systems; including, as appropriate, the gathering, analysis, and preservation of evidence, as well as the development and implementation of necessary countermeasures.
- Responsible for handling digital forensic evidence and analyzing various digital devices with EnCase 6/7 Forensic Software and FTK Imager.
- Trained resource staff in reviewing and distributing industry vendor alert analysis/recommendations expanding continuous coverage during task assignments.
- Monitors the Department of Labor (DOL) Lockup press room to detect, locate, and monitor all cellular, Wi-Fi, and Bluetooth activity to prevent the early release of BLS embargoed data in the room
- Serves as a leading BLS technical authority/resource for IT security by providing sound guidance, comment, and advice at internal and external settings of various types, including conferences and intra-agency groups. In addition, the expertise is used in ensuring the organization's review of all BLS proposals for new and modified IT systems and procedures to ensure and certify their adherence to required IT security requirements and best practices in the ever changing IT security field.
- Participates in network and systems design to ensure incorporation and implementation of appropriate systems security controls and policies, which ensures the confidentiality, integrity, and availability of systems, networks, and data through the planning, analysis, development, implementation, maintenance, and enhancement of information systems security programs, policies, procedures, and tools.
- Participates in the execution of annual third-party security assessments. These assessments typically include the use of external experts in the field of IT security in auditing key components of the Bureau's environment to ensure that they are configured in compliance with Federal statute and regulation.
- Assists division management in their efforts to prepare IT security policy by performing discrete tasks associated with the overall policy development process, such as evaluating and recommending adoption, nonuse, or use with modification of new or enhanced approaches to the operation of BLS IT systems.
0-5 years of experience
- Monitoring network traffic, opening investigations for infected workstations.
- Investigating spam emails and responding to security inquiries from users.
- Processing data loss prevention (DLP) cases.
- Opening incidents for DOS Attacks.
- Training new specialists on SOC processes.
0-5 years of experience
Systems Administrator
- Administrated several Systems and Active Directory, DNS, DHCP, SQL Server, Microsoft Exchange.
- Installed, Configured and Troubleshoot Computer Hardware and Software.
- Help Desk Specialist managing more than 100 users in the Company.
- Computer Security Analysis.
- Set parameters of Enterprise Informatic Security.
- Worked with Security and Analyst Software for Enterprise Security.
- Implemented Information Security rules.
- Network scanning and configuration of Firewalls and Software of monitoring.
Information Technology Cover Letter Examples